Aug 21, 2019 | RIsk Management News
Originally posted on Insurance Business America by Alicja Grzadkowska.
Despite the onslaught of natural disasters and cyber incidents seen in the past year, many people are still unprepared for dealing with crises. It’s not just the 83% of homeowners who are vulnerable to hurricanes, flooding, and other weather events because of a lack of preparedness – even global multinationals don’t necessarily have plans in place should they have to deal with a major hit from a storm or hacker, according to one expert.
“At least 50% of companies have a limited to no grip on the business implications of a cyber attack on their day-to-day operations. They’re thinking about it as an IT problem,” explained David Nolan, CEO and founder of Fusion Risk Management, a provider of business continuity and risk management solutions. “They’re not thinking about it as a business problem.”
Take Facebook, said Nolan. If companies were good at having foresight about potential crises, the social media giant’s leaders would’ve been able to predict the fallout of providing such widespread access to its users’ data. And when it comes to nat cats, organizations are still using spreadsheets and static documents that don’t lend themselves well to maintaining and incorporating accurate forecasting and analytics, said Nolan.
“There’s a lot of forgiveness in this world for acts of god and cyber attacks because everybody has to face them, but I don’t think there’s a lot of tolerance for people being unprepared and not having given it significant thought,” he said.
Just as corporations will want to stay on top of what’s new in technology and find ways to incorporate tools to cut down on costs and increase efficiency, understanding what’s cutting edge in risk management and business continuity planning is likewise crucial to preventing losses and protecting a company’s reputation.
“We’re the ones protecting the brand equity – the things that are essentially uninsurable – while the insurance companies are covering their part of that,” explained Nolan. “Ours is a management system for managing these risks to avoid them or to be able to respond effectively in the event that one of them happens.”
Fusion thinks about business continuity and resilience using four scenarios: workplace disruption, workforce disruption, supply disruption or technology disruption. Acts of terrorism or volcanic eruptions and any kind of catastrophe in between could result in one of these situations.
Companies should be thinking about what happens if they lose a key asset or location, and what operations would be impacted, as well as how that loss would materially affect their ability to deliver products and services, according to the CEO. Fusion can help simulate that potential fallout and, when a risk becomes reality, provide answers on how to manage it instantaneously.
“If an executive is trying to deal with a crisis, we’re going to know exactly what happened, we’re going to know what the direct damages are, we’re going to know what the collateral damages are, we’re going to know what our resources are, we’re going to know what our expectations should be because we will have simulated an actual response,” said Nolan.
One example of a Fusion client that dealt with a problem and was able to avoid major losses was a business in Florida that was preparing for the approaching hurricane, which could’ve come across the Gulf, the west coast of the state or the east coast and hit the Carolinas.
“They were able to model those scenarios in advance and, before the hurricane hit, they were able to make adjustments in where their products were shipped,” said Nolan. “They adjusted their logistic operations and they essentially kept all of the supply assets outside of the impact zones, and essentially avoided any disruption because they didn’t continue to move product or supplies or even people inside an area that was potentially going to get hit.”
Fusion works with some of the largest companies in the world and counts around 80 Fortune 500 firms among its clientele, along with many companies as small as 500 employees or less. The team has seen firsthand how important having a plan in place, besides just property and casualty insurance or business interruption coverage is to a company’s brand.
“Those things don’t protect the covenant of trust that an organization has with their customers, and so that’s where we come in,” said Nolan. “How do we protect the brand and how do we protect the covenant of trust that an organization has?”
Jul 31, 2019 | RIsk Management News
Originally posted on Raconteur by Nick Easen.
The aftermath of a global corporate scandal is a very messy affair. Firstly, there’s the breaking news, then the media frenzy, the plummeting share price, the evaporating confidence, the damage-limitation exercises and finally the groveling executives. We live in a super-charged, hyper-connected environment, answerable to the 24-hour “churnalism” cycle and social media chatterati. Boeing, Uber, Nissan, Huawei, Airbus or Purdue Pharma, to name but a recent few, have all had to step up like Winston Churchill to their darkest hour. “Crisis management can be like dealing with an explosion,” explains Jo Willaert, president of the Federation of European Risk Management Associations.
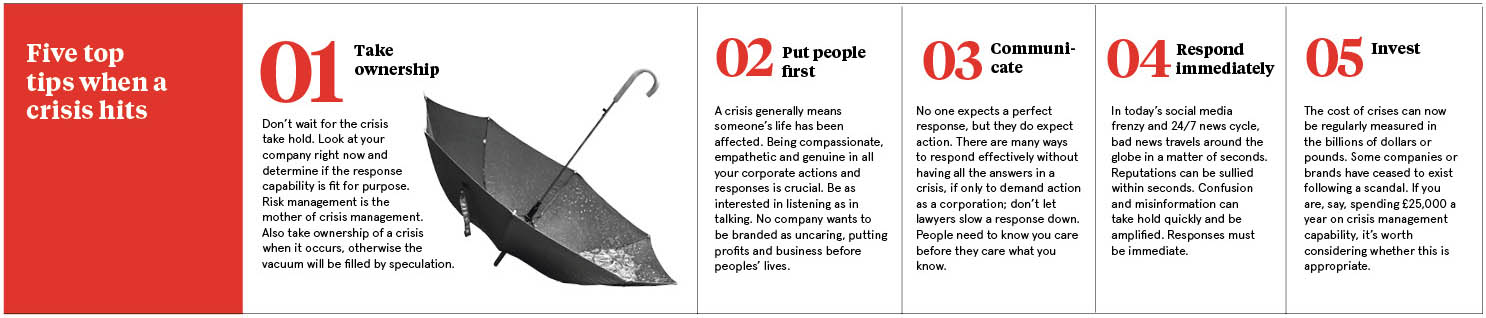
Be quick, honest, open and, in such circumstances, be compassionate in communications, these are the key principles of crisis management
And with any explosion, corporate or otherwise, everyone ducks away from the line of fire for fear of getting hit. Damage limitation can trump open communication. Slow and myopic group-think can stymy a crystal clear, crisis management plan because the stakes can be excruciatingly high and the fallout unthinkable. No one really wants to spark the next Lehman or Enron crisis. It would be career suicide.
Why do companies need a crisis management plan?
“Be quick, honest, open and, in such circumstances, be compassionate in communications, these are the key principles of crisis management,” says Julia Graham, deputy chief executive of Airmic, the UK’s risk management body.
Yet time and again these messages don’t seem to permeate the rarefied air of boardrooms or the upper corporate classes, and it shows. Whether it’s Boeing’s chief executive taking a week to respond to the fatal Ethiopian Airlines crash or BP’s boss Tony Hayward making a quip during the Gulf of Mexico oil spill saying he “wanted his life back”. The rapid, heartfelt response to an incident is as crucial today as it was ten years ago.
“An actual crisis is a pressure cooker and no time to start working out roles, responsibilities, and processes for your management team. Yes, Mr. Hayward apologized quickly, yet the damage was done and here we are almost a decade later still talking about it,” says Marc Cornelius, founder of 8020 Communications, a specialist public relations consultancy.
At the heart of every response is an effective crisis response plan. Businesses are most resilient when they’ve already considered what to do if the worst happens and if all executives understand the roles they need to play. A risk manager co-ordinates decision-making teams that need to be multi-disciplinary, with all business functions represented, since they see situations from diverse angles.
“For instance, a classic tension can exist between legal and marketing perspectives: saying very little might theoretically limit your potential liability, but will the consequent damage to your brand end up costing you more long term? You can bet those functional tensions would have been going on recently within Boeing,” says Mr. Cornelius.
Why strong leadership is crucial in crisis management
Time and again though companies are caught up in a crisis storm that is hard to weather. Facebook had its Cambridge Analytica moment, while Monsanto had to deal with a customer allegedly contracting cancer from its weedkiller, then there was Exxon’s reaction to the Alaskan oil spill, the list goes on. The lessons that can be learned are legion. Each event is unique and complex.
Rupert Younger, director of the Oxford University Centre for Corporate Reputation, thinks we need to go beyond our preparation manuals, rehearsals, box-ticking exercises, and well-documented crisis management plans, and instead, create more of a wider culture of being able to respond to crises.
“Smart companies should spend as much time listening as talking, empathy, and humanity are crucial. Each stakeholder has to feel well informed and properly looked after at all times, and internal teams need to be organized and focused on this,” says Mr. Younger.
One thing that a lot of crisis experts agree on is the crucial role that executive leadership plays in dealing with a crisis. Like the logjam over Brexit, markets and corporations look for certainty, any perceived loss of control, lack of solutions or uncertainty can cause real harm, especially in the early stages of an incident, and a lot of direction comes from the top.
A responsive C-suite is the new imperative, especially when key executives are increasingly being held accountable if their company is not able to respond to a crisis. Look at various governments’ response to the live-streamed mosque attacks in New Zealand and their crackdown on social media companies for showing harmful content, from Australia to the European Union, including the UK.
Sound risk management leads to greater trust
When management could be personally liable for these crises and fines could reach as high as 4 per cent of global turnover, as is the case under the EU’s General Data Protection Regulation, it’s enough to make any corporate board, from Twitter to YouTube, rewrite their crisis management plans and think twice about how they respond.
“Yet events usually outpace responses and without preparations or expertise at the table, leadership can find themselves frozen as they watch things unfold. The organization needs to be clear on who takes the lead in efforts to restore the confidence of the public, clients, employees, and investors,” says Erik Petersen, head of crisis management consulting in Europe at Control Risks.
“The issue is that leaders will often be required to make decisions with insufficient information. It can take days or sometimes longer to get facts or understand the nature of the problem, while stakeholders will demand immediate answers and response.”
The fact is most of us trust corporations around the globe without knowing what kinds of systems they have in place to deal with risk, safety, and incidents that involve people’s lives, health and wealth. We eat, fly, drink, drive and consume various products from countless companies that we put our utmost faith in. The question is, can we really trust them?
“Companies that manage risk well tend not to face crises of their own making,” says Sandra Sucher, professor of management practice at Harvard Business School. “In my research, I’ve found a close association between sound risk management and being trusted. Risky actions lead to mistakes of many kinds, and we mistrust, with good reason, companies which don’t seem to appreciate the consequences of their mistakes and fail to anticipate the risks that things could go wrong.”
Why you cannot ignore crisis communication management
Another aspect that’s crucial is crisis communication and the language used. “It is arguably becoming one of the most important elements of damage limitation in an era where harm to brand and reputation is the greatest part of the impact,” says Mr. Petersen.
Increasingly, big corporations value the role of crisis communications, they also understand that it’s a specialized skill either to be cultivated in-house or via an outside consultant who knows the business well and is on call. “Those organizations that don’t value communications, do so at significant risk,” says Kelli Matthews, senior instructor at the School of Journalism and Communications, University of Oregon.
Many crises that whip through the media are hardly binary affairs, they are infinitely complex. The key is to make these issues simple and communicate in plain, unambiguous language. “This can be really challenging,” says John Martin McDonald, founder of Caeli Communications. “As Mark Twain once said: ‘I didn’t have time to write you a short letter’. But you must make the effort and do it throughout the crisis.”
Reputational damage may be significant, if not permanent
All this underplays the role of the risk manager, yet they are a crucial go-to person in any crisis. They have a pivotal role to play since the impact of a crisis can touch many facets of a business from customers to shareholders, affected communities to supply chains.
“The professional risk manager serves as a coordinator across many functions that need to be involved in a situation like this, both for the manufacturer and the airlines in the case of the Boeing crisis,” says Typhaine Beaupérin, chief executive of the Federation of European Risk Management Associations. “The risk professional will also play an important role in managing the complex insurance issues that will inevitably arise as a result of a crisis.”
It’s not all doom and gloom. Many businesses can be resuscitated over time. “A company’s reputation is not earned overnight and, usually, not lost overnight,” says Marc Szepan, a lecturer at the University of Oxford Saïd Business School.
But beware, a recent study by The Economist of the eight most notable corporate crises since 2010, including those at Uber and Wells Fargo, found that the median firm was worth 30 percent less today than it would have been had the scandals not occurred. Ouch.

Jul 17, 2019 | RIsk Management News
Originally posted on Mark On Solutions by Matt Davis.
The insurance industry uses the term “risk appetite” to describe the level of risk that an organization is willing to accept. An essential first step in managing corporate security, and resiliency, has to do with determining your firm’s risk appetite.
Risk appetite is defined as the amount of risk exposure that an organization is willing to accept as a normal course of business. Tolerance for risk exposure can vary greatly from one company to another, and among different industry segments.
As a precursor to establishing an effective risk management program, it’s essential for a firm to determine its risk appetite. This can be done using a baseline analysis that accounts for a combination of threats, vulnerabilities, consequences, and readiness.
It’s interesting to note that often a company’s appetite for risk doesn’t match its actual exposure. In other words, companies are often unaware that their risk exposure is significantly greater that their actual tolerance for that risk.
Assessments, training, and exercises are all excellent ways to expose those gaps and establish focus points for adjusting your firm’s security posture to align with its risk appetite.
Jul 10, 2019 | RIsk Management News
Originally posted on BlueDrop by Colin McCabe.
Whilst risk management played a role in business prior to the financial crisis of 2007-2008, it didn’t have quite so much of a major importance as it does today. These days, if a company doesn’t find a way to prevent or mitigate risk then it can really struggle to get back on track. Unexpected risks can shut down a business for days and sometimes even longer, many never even re-open.
Despite the scary facts, it is thought that 75% of businesses today still don’t have a risk management plan in place. Whilst there are many forms of risk management insurance can be one the most important as it helps to prevent losses, and as we all know fewer losses mean higher profits.
How we can help your Risk Management
At Bluedrop Services risk management is taken seriously and we endeavor to meet our client’s requirements to achieve maximum profitability with minimum risk to them. We have implemented a specialist risk management department which will strive to succeed in aiding clients in the process of risk management and how to reduce risk.
Risk management is the identification, assessment, and prioritization of risk followed by coordinated and economical application of resources to minimize, monitor, and control the probability of any unfortunate events, which can occur at any time. The objective of risk management is to assure a company/task does not deflect from achieving its goals.
Risks can come from various sources depending on your type of business, these can include; road risk, potential failure of projects, legal liabilities, financial risk, accidents, deliberate attack, incorrect or no process and procedures, and poor health & safety policies. All of which could have a serious financial impact on a business or body.
Where should you focus your Risk Management?
Emerging companies should focus in particular on employer’s liability, data privacy and cyber liability, errors and omissions liability, directors’ and officers’ liability (D&O) and, depending on the number of employees, fiduciary liability and employment practices liability policies. By identifying and assessing risk early this will reduce the chance of a potential financial impact on a business.
How to reduce your risk
Strategies to manage risk typically include avoiding the risk, reducing the negative effect or probability of the threat, transferring all or part of the risk to another party, and even retaining some or all of the potential or actual consequences of a particular risk.
Although risk management has no measurable improvement on risk there is an increase in confidence in the decisions made by risk management strategies.
Simple risk assessments can be completed to reduce any type of risk, these should include:
1. What is the threat/risk
2. Who is exposed and why
3. Current process
4. What can be done to reduce the exposure
5. Documentation of the above
Sensible risk management is about taking practical steps to protect people from real harm and suffering not bureaucratic back covering. Taking a sensible approach to risk management is about ensuring the safety of employees and public, learning & understanding by all and responsibility of risk by companies.

Jun 19, 2019 | RIsk Management News
Originally posted on ClearRisk by Rebecca Webb.
An average organization only uses 50% of its available data for decision-making. This is significant when you consider 70% of late adopters base their decisions on gut feeling or experience, while 60% of best-in-class companies use data analytics when making decisions.
Data is powerful when used to its full capability; by using all available data, an organization can establish a clear competitive advantage. Storing and regularly accessing relevant information will allow your organization to save time and money while drastically improving decision quality. Below are some of the key benefits that data utilization can have on your organization.
1. Increased efficiency
In a well-established organization, it’s easy to continue doing a task the same way out of habit and convenience. Without referencing data, you may get stuck in a routine and not recognize internal flaws. Streamlining people, processes, and tasks will increase efficiency across the organization.
2. Better decision making
Analyzing your data will provide the information required to run the organization, such as what course of action is necessary and whether your strategies have been successful. To do this, you need to have the right kind of data; ensure that you collect relevant, accurate, and complete information.
The more data you store, the more information you will have to base your next decision on. This can lead to more creative and smart strategies as well as help you choose positive risks and pursue paths that will lead to growth.
3. Financial health
Using data effectively will allow an organization to save money. By consistently tracking and monitoring costs, prices, and other useful information, you can track when spending is higher than it should be. It can also flag problem areas or help you identify costs that you shouldn’t be incurring. Further, making a habit of storing data means you will have a quick and easy process if you are ever audited or when entering tax season.
4. Making a case for any project
No matter the business idea, there needs to be some data and information to support it. By accessing stored information, you will be able to analyze data and use it to support a proposed project. With the collected data, you will be able to present your case to supervisors or employees to prove that the decision would benefit the organization.
5. Increased accountability
Without storing data, it can be difficult to know when something isn’t as it should be. A thorough database can allow management to recognize signs of fraudulent activity. It will show employees that they are being monitored, increasing their accountability and ethical actions. If something does go wrong, your organization will be able to show it had some measures in place to try and prevent the incident, thus protecting brand reputation.
6. Preventative measures
Having data allows you to analyze it. This will let you identify and mitigate against threats, reduce repetitive losses and lawsuits, and even lower insurance premiums. For more detail about the benefits of data analytics, check out our next in-depth blog post!
Feb 27, 2019 | RIsk Management News
It is not a risk-free proposition for nonprofit boards to make investment decisions that meet philanthropic goals. This is all the more difficult for those trustees without a background in finance. The simple answer is usually to allocate the investments conservatively and rebalance periodically to at least beat inflation and preserve capital. Large charities like university endowments turn to more sophisticated methods of portfolio diversification, expanding beyond stocks and bonds into vehicles like hedge funds, private equity, venture capital, and real estate.
The Conversation’s detailed article cautions that it is not enough to focus only on returns; in fact, it’s more important to consider risk-adjusted returns. In the case of digital currencies, it would have required nerves of steel for trustee investment committees to commit to pre-established decision-making processes to avoid the bitcoin crash in early 2018, after it rose by 1,318 percent against the US dollar in 2017.
These gains gave way to massive losses in the first eight months of 2018, when digital currencies plunged more sharply than the dot-coms crashed in the early 2000s.
Some charities that received massive cryptocurrency donations in 2017 may not have been able to convert them into regular money before they lost much of their value the next year. Silicon Valley Community Foundation, for example, disclosed in its 2017 audit report that for more than 45 percent of its investment assets, restrictions would prevent them from being converted to cash at any point in 2018.
The fact that charities only disclose their financial data once a year means that the scale of their at-risk wealth, as of now, is unknown.
There are more reasons than volatility to be concerned about holding onto investments of cryptocurrencies. Wallets and exchanges used to hold the investments can be hacked. Compliance issues abound. Regulators are still catching up to the IRS ruling in 2014 that treated digital currency as a form of investment property. The sweeping new tax billpassed into law last December may bring more change. Inasmuch as digital money ledgers for transactions are owned and maintained by the users of the systems rather than controlled by a government or a central bank, it is difficult to predict how government will eventually choose to manage this revolutionary type of money.
The Conversation article goes on to examine other forms of appreciated assets being given by a shrinking group of ever-wealthier donors and the “charitable middlemen” needed to help facilitate these donations.
Fidelity Charitable got 61 percent of its donations in assets other than cash in 2017. Other prominent donor-advised fund sponsors saw a similar result. Schwab Charitable obtained over 70 percent of its 2017 donations in non-cash assets. In the last month of the year, that figure was 80 percent for Vanguard Charitable.
These fast-growing charities bring a key skill: harvesting capital gains. That is, they accept tax-advantaged donations, hold onto that wealth, and—in most cases—transfer the money derived from those assets to the donor’s charities of choice when the donor asks.
For nonprofits, it could be said that today’s donor classes are creating as many challenges as solutions. As government funding continues to diminish for many of the issues addressed by the nonprofit sector, private philanthropy becomes all the more important, and along with it, the skills to properly raise, receive, and manage the forms and flavors in which it is given.
Author: Jim Schaffer
Source: Nonprofit Quarterly